In this post, we’ll talk about configuring the NetScaler to use an external authentication mechanism, specifically LDAP. The NetScaler can support several external authentication methods, such as RADIUS, LDAP, TACACS, and NT4/NTLM.
Using an external authentication mechanism will allow you to manage access to the NetScaler and its resources using your existing user management tools.
In this example, we want to create a new Active Directory group NSAdmins and allow that group to manage the NetScaler. LDAP can also be used to grant permissions to the Access Gateway (SSL VPN).
The high level steps are as follows:
1. Create an Active Directory security group called “NSAdmins”
(Steps 2-5 on the NetScaler)
2. Create a local group called “NSAdmins” (match the names exactly)
3. Create an LDAP server object
4. Create an authentication policy
5. Bind the authentication policy
6. Add AD Users to the NSAdmins security group
7. Test login with AD credentials
I’m going to assume you know how to create an Active Directory group and get right into the NetScaler steps:
Configuring Active Directory Authentication on the NetScaler
a. Login to the NetScaler and expand System.
b. Click Groups | Add
c. Create the local group NSAdmins and specify the rights for this group
d. Remaining under the System options, click Authentication.
e. Click the Servers tab and then Add
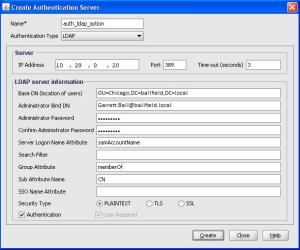
f. Enter the following information:
Name
Enter a name for the authentication server object
Authentication Type
LDAP
IP Address
IP Address of the LDAP Server
Port
389 is the default LDAP Port but you can use 636 for secure LDAP
BaseDN
This represents the Distinguished Name of the starting OU. Example: OU=Chicago,DC=ballfield,DC=local
Administrator Bind DN
Though the option says Administrator, this can be any user with the permissions to browse the directory. This value can be a distinguished name or an Active Directory UPN such as garrett.ball@ballfield.local
Password
Enter the password for the account specified.
For this example, all other values can remain at their default.
g. Click Create to complete the authentication server object
h. Remaining in the Authentication subnode, click the Policies tab.
i. Click Add
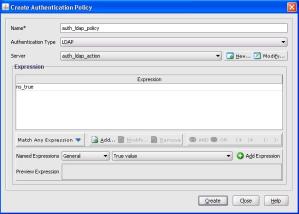
j. On the Create Authentication Policy window, enter the following information:
Name
Enter a name for the authentication policy
Authentication Type
LDAP
Server
Specify the NetScaler LDAP server object just created
Expression
Specify “ns_true” as the expression
k. Click Create
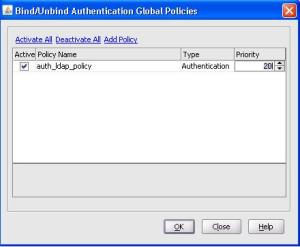
l. Still on the Policies tab, highlight the newly created policy and click Global Bindings
m. On the Bind/Unbind Authentication window, mark the LDAP policy as Active, set a priority value, and click OK.
Finally, add the appropriate Active Directory users to the AD based NSAdmins group and test access to the NetScaler.


thanks man.. totally helpful!
Thanks, I couldn't find this anywhere. Do you have one for radius as well?
Thanks…top result on Google and saves me a Citrix sign in 😉